A2A Protocol vs AuthSmith
A2A Protocol
A2A Protocol enables seamless collaboration among AI agents across diverse platforms, enhancing their collective.
Last updated: February 28, 2026
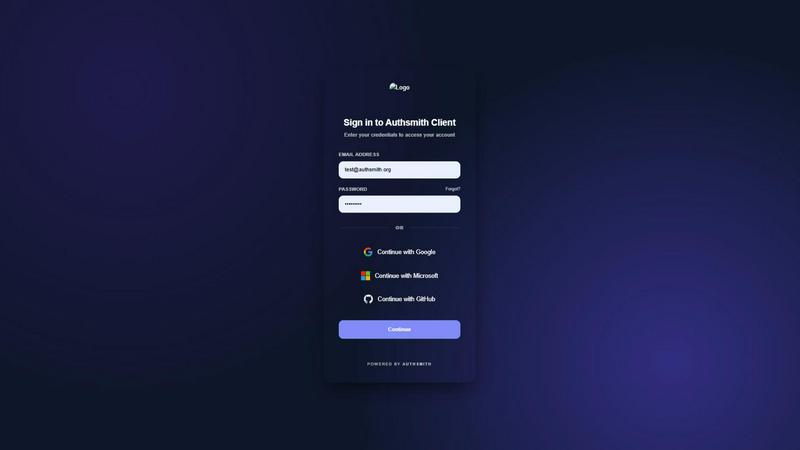
AuthSmith
AuthSmith is your secure, scalable identity infrastructure that integrates in minutes.
Last updated: February 28, 2026
Visual Comparison
A2A Protocol
AuthSmith
Feature Comparison
A2A Protocol
Universal Interoperability
A2A Protocol enables AI agents to collaborate seamlessly across different platforms and frameworks. This universal interoperability is crucial for organizations that rely on diverse technologies, allowing them to maximize the effectiveness of their AI systems without the constraints of compatibility issues.
Enterprise-Grade Security
Security is paramount in the realm of AI communications. A2A Protocol is built with enterprise-grade authentication and authorization, incorporating robust security measures that align with OpenAPI's authentication schemes. This ensures that data exchanges between agents are secured against unauthorized access.
Flexible & Scalable
Whether you're managing quick tasks or executing long-running research projects, A2A Protocol supports a wide range of applications. Its flexible architecture allows for real-time feedback and state updates, ensuring that agents can adapt to changing requirements and workloads efficiently.
Multi-Modal Support
A2A Protocol embraces the future of communication by supporting multiple modalities, including text, audio, and video streaming. This multi-modal capability enhances the richness of interactions between agents, making it suitable for complex scenarios that require diverse forms of data processing and communication.
AuthSmith
Centralized User Management
Effortlessly manage your entire user base from a single, intuitive dashboard. Create, update, and deactivate user accounts, assign roles and permissions, and configure authentication settings without touching backend code. This centralized control simplifies administration and provides a clear overview of your user ecosystem, saving you countless hours of manual management and database queries.
Advanced Security & Automated Alerts
Go beyond basic passwords with enterprise-grade security features. AuthSmith includes Multi-Factor Authentication (MFA), checks user passwords against known data breaches, and offers session controls like geo-fencing. Crucially, its automated security alert system notifies you instantly of suspicious login attempts or failed authentications, allowing you to proactively respond to potential threats.
Seamless Login Methods & SSO
Offer your users a frictionless login experience with support for all major methods. Integrate email/password, popular social logins (like Google or GitHub), and powerful Single Sign-On (SSO) for enterprise customers. This flexibility improves user onboarding, reduces password fatigue, and allows you to cater to both consumer and B2B audiences with one unified platform.
Robust API Access & Integrations
Build AuthSmith seamlessly into your unique application flow with its comprehensive, developer-friendly APIs. Enable custom authentication workflows, sync user data with your other services, and leverage pre-built components for faster frontend integration. This ensures AuthSmith adapts to your stack, rather than forcing you to adapt your development process to it.
Use Cases
A2A Protocol
Collaborative AI Development
In the world of AI development, A2A Protocol enables teams to create and deploy intelligent agents that can communicate across various platforms. Developers can build applications that leverage the strengths of different agents, enhancing overall functionality and user experience.
Automated Customer Support
Companies can utilize A2A Protocol to create AI-driven customer support systems where multiple agents collaborate to address customer inquiries. This results in faster response times and more comprehensive assistance, improving customer satisfaction and operational efficiency.
Research and Data Analysis
For researchers, A2A Protocol provides a framework for AI agents to work together on complex data analysis tasks. By allowing agents to share insights and findings in real-time, organizations can accelerate research timelines and improve the quality of their outcomes.
Smart Home Integration
A2A Protocol can revolutionize smart home applications by enabling different AI agents, such as those controlling lighting, security, and climate control, to communicate and collaborate seamlessly. This integration creates a more responsive and user-friendly smart home experience.
AuthSmith
Rapid MVP Development for Startups
A startup building its minimum viable product needs to validate its idea quickly. AuthSmith allows founders to integrate a full-featured, secure authentication system in minutes. This lets them bypass weeks of complex auth development and focus engineering resources on core product features, accelerating time-to-market and user testing without security compromises.
Scaling SaaS Applications
As a B2B SaaS application grows, its authentication needs become more complex. AuthSmith scales effortlessly, providing the advanced features needed for larger teams, such as Role-Based Access Control (RBAC) for internal permissions, Enterprise SSO for corporate clients, and detailed analytics to monitor platform adoption and user behavior.
Enhancing Security for Established Apps
An existing application with a custom-built or outdated auth system is a security liability. AuthSmith offers a secure migration path ("lazy migration") to modernize the identity layer. Teams can bolster security with MFA, breach monitoring, and automated alerts without a disruptive, full-scale rewrite, immediately improving their security posture.
Building Consumer-Facing Mobile & Web Apps
For apps targeting a broad consumer audience, user experience is paramount. AuthSmith’s pre-built UI components and support for social logins (Google, Apple, etc.) make sign-up and login seamless. Features like session management and secure data storage ensure a smooth and trustworthy user journey from first visit to regular engagement.
Overview
About A2A Protocol
A2A Protocol is an innovative open standard designed to facilitate seamless communication and collaboration among AI agents across diverse platforms and frameworks. This cutting-edge technology empowers intelligent agents to work together efficiently, regardless of their underlying technologies. Targeted at developers, enterprises, and AI researchers, A2A Protocol unlocks the potential of agentic AI by fostering true multi-agent scenarios. Its main value proposition lies in universal interoperability, ensuring that AI agents can interact and share information effortlessly. With features like enterprise-grade security, flexible scalability, and robust support for various data modalities, A2A Protocol paves the way for enhanced collaboration in AI applications, ultimately driving innovation and efficiency in a rapidly evolving digital landscape.
About AuthSmith
AuthSmith is the identity infrastructure built for modern developers who need to move fast without cutting corners on security. It's a complete, secure, and scalable authentication solution that removes the immense pain of building auth from scratch. In today's app landscape, authentication is foundational but notoriously complex—difficult to implement securely, time-consuming to integrate across platforms, and dangerously easy to misconfigure. AuthSmith solves this by providing a powerful, drop-in solution that lets your team integrate robust user management in minutes, not months. Designed for startups and growing businesses, it handles everything from simple email/password logins to advanced Single Sign-On (SSO), multi-factor authentication (MFA), and granular role-based access control. With AuthSmith, you can focus on building your next big idea's core features, while we ensure your user identity layer is secure, private, and ready to scale from day one. It's the secure foundation your application deserves.
Frequently Asked Questions
A2A Protocol FAQ
What is the A2A Protocol?
A2A Protocol is an open standard that allows AI agents to communicate and collaborate seamlessly across different platforms and frameworks, enhancing interoperability and functionality.
How secure is A2A Protocol?
A2A Protocol is designed with enterprise-grade security, employing robust authentication and authorization mechanisms that comply with OpenAPI's standards to protect data exchanges between agents.
Can A2A Protocol support various AI modalities?
Yes, A2A Protocol supports multi-modal communication, including text, audio, and video streaming, making it versatile for a wide range of AI applications.
Who can benefit from using A2A Protocol?
A2A Protocol is beneficial for developers, enterprises, and researchers looking to enhance the collaboration of AI agents across various platforms and frameworks, maximizing the potential of agentic AI solutions.
AuthSmith FAQ
How quickly can I integrate AuthSmith into my project?
You can have a basic authentication flow up and running in as little as 5 minutes! Our detailed Quickstart guide and pre-built UI components are designed for rapid integration. Simply add our SDK to your project, configure your settings in the dashboard, and you'll have a secure login system ready for users in no time.
What happens if I exceed my plan's user limit?
Our Starter and Free plans have monthly active user (MAU) limits. If you exceed your plan's limit, your service will continue to function without interruption. We will notify you and provide a grace period to upgrade to a higher tier that accommodates your growth, such as the Professional or Enterprise plan, which offer unlimited users.
Is my users' data secure and private with AuthSmith?
Absolutely. Security and privacy are our top priorities. All sensitive user data is encrypted at rest and in transit. We adhere to industry best practices and compliance standards. Furthermore, our Enterprise plan offers the option to use your own database, giving you full control over your data's physical storage location.
Can I customize the login UI to match my app's branding?
Yes! While our pre-built components offer a great starting point, you have full control over the look and feel. You can disable AuthSmith branding and apply your own CSS for complete customization. For deeper integration, our robust APIs allow you to build a fully custom frontend experience while leveraging our secure backend infrastructure.
Alternatives
A2A Protocol Alternatives
A2A Protocol is a cutting-edge solution that falls within the Productivity & Management category, specifically designed to empower AI agents to collaborate seamlessly. This innovative protocol enables standardized communication between intelligent agents, ensuring that they can work together effectively to achieve complex tasks and enhance overall productivity. Users often seek alternatives to A2A Protocol due to various factors such as pricing, feature sets, or specific platform needs that may not align perfectly with their requirements. When exploring alternatives, it’s essential to evaluate critical aspects like compatibility with existing systems, the scalability of the solution, customer support, and the overall user experience to ensure the best fit for your organization’s goals.
AuthSmith Alternatives
AuthSmith is a secure, drop-in authentication service that belongs to the web development and software tools category. It solves the foundational but complex challenge of building secure user login systems from scratch, letting development teams move fast without compromising on safety. Developers often explore alternatives for various reasons. Needs can differ based on project scale, specific feature requirements like social logins or multi-factor authentication, budget constraints, or the need for a platform-specific solution. The search for the right fit is a normal part of building a robust tech stack. When evaluating options, key considerations include security posture and compliance certifications, ease of integration with your existing frameworks, scalability for future growth, transparent and predictable pricing, and the quality of developer documentation and support. The goal is to find a solution that is both powerful for engineers and invisible to your end-users.
