RankInPublic vs Threat Modeling
Last updated: March 11, 2026
Last updated: February 28, 2026
Visual Comparison
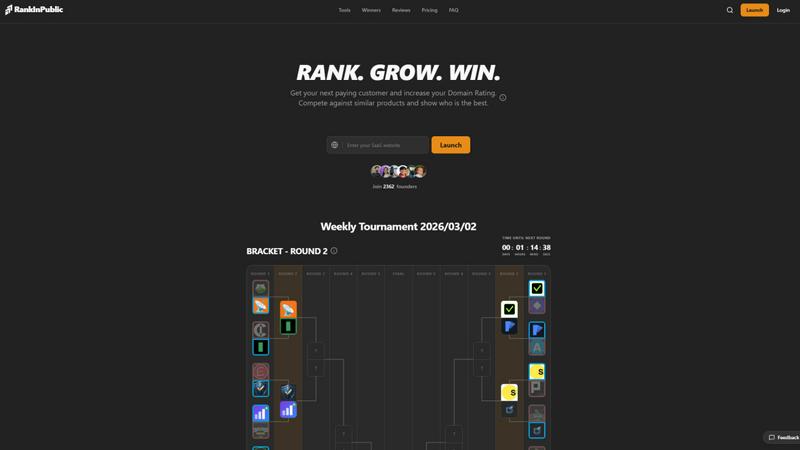
RankInPublic
Threat Modeling

Feature Comparison
RankInPublic
Daily Tournaments
Every day, RankInPublic hosts a thrilling tournament where new products face off against one another in exciting matchups. This structure encourages competitive spirit and provides creators with immediate feedback from the community, driving engagement and visibility.
Community Voting
RankInPublic empowers its users by enabling them to vote for their favorite projects. This participatory model not only amplifies user involvement but also ensures that the most innovative and promising products gain the recognition they deserve.
Instant Product Launch
Submitting a product to RankInPublic is a breeze. Creators can launch their projects instantly, gaining immediate exposure on the platform. This rapid onboarding process is perfect for early-stage startups looking to make a splash in the market.
Featured Spotlights
Winning a tournament on RankInPublic comes with the added benefit of being featured across the platform. This spotlight not only boosts visibility to a larger audience but also enhances credibility, helping startups to establish a strong foothold in their respective niches.
Threat Modeling
Powerful Assessment Engine
Our powerful assessment engine allows users to understand potential threats and security weaknesses effectively. It evaluates the system architecture, identifies vulnerabilities, and helps prioritize risks based on their impact and likelihood, ensuring that organizations can focus on what matters most.
Flexible Diagram Engine
The flexible diagram engine enables users to visualize components and communication flows seamlessly. This feature aids in representing complex systems intuitively, allowing teams to collaborate and communicate effectively about security concerns and design choices.
Clear Reporting and Metrics
Our tool provides clear reporting and metrics that are essential for compliance demonstration. Users can generate detailed reports that outline identified threats, mitigations, and risk assessments, helping organizations maintain transparency and accountability in their security practices.
Extensive Resource Library
We offer a comprehensive resource library filled with articles, templates, and real-world examples to support users in their threat modeling journey. This library is designed to educate teams on various threat modeling methods, ensuring that they are well-equipped to tackle security challenges efficiently.
Use Cases
RankInPublic
Product Validation
Indie hackers can use RankInPublic to validate their startup ideas by gauging community interest and feedback. By participating in tournaments, creators can receive constructive insights that help refine their offerings before a broader launch.
Audience Building
RankInPublic serves as an effective tool for building an audience. By competing in tournaments, creators can attract potential users who are genuinely interested in their products, fostering a community of early adopters.
Networking Opportunities
The platform connects indie developers with like-minded creators and potential collaborators. By participating in tournaments and engaging with the community, users can network, share ideas, and collaborate on future projects.
Trend Discovery
For users seeking to stay ahead in the tech landscape, RankInPublic is an invaluable resource for discovering emerging trends. By regularly checking tournament outcomes and featured projects, users can identify the next big innovations before they hit the mainstream market.
Threat Modeling
Early Detection of Vulnerabilities
By employing threat modeling during the design phase, teams can identify and address vulnerabilities before they escalate into costly security incidents. This proactive approach minimizes risk and reinforces security from the outset.
Streamlining Compliance Efforts
Organizations can use Threat Modeling to demonstrate compliance with industry standards and regulations more effectively. The tool's reporting features provide the documentation needed to showcase security efforts to stakeholders and regulatory bodies.
Enhancing Collaboration Among Teams
Threat Modeling fosters collaboration between development and security teams by providing a common framework for discussing threats and mitigation strategies. This shared understanding enhances communication and aligns security objectives with business goals.
Integrating Security into DevOps Processes
With the rise of DevOps practices, integrating threat modeling into the continuous integration and continuous deployment (CI/CD) pipeline ensures that security remains a priority throughout the software development lifecycle, rather than an afterthought.
Overview
About RankInPublic
RankInPublic is an innovative platform tailored specifically for indie hackers and digital creators who aspire to showcase their groundbreaking products in a vibrant, competitive tournament-style environment. Every day, new projects engage in head-to-head matchups, allowing community members to vote for their favorites and discover the freshest tools emerging within the tech ecosystem. This gamified approach not only enhances visibility for early-stage startups but also enables founders to validate their concepts and expand their user base through genuine, organic engagement. Unlike traditional directories that often lack dynamic interaction, RankInPublic thrives on daily momentum and real-time feedback from the community, fostering a lively arena where quality and innovation are paramount. It serves as the ultimate hub for anyone eager to support indie developers or uncover the next big trend in technology while participating in an exhilarating competition.
About Threat Modeling
Threat Modeling is a proactive approach in cybersecurity that focuses on identifying, understanding, and mitigating potential threats during the design phase of software development. By integrating security into the development lifecycle, organizations can prevent vulnerabilities from being introduced, thereby adopting a "security by design" philosophy. This tool is designed for developers, security teams, and organizations aiming to enhance their security posture without compromising agility. The main value proposition of Threat Modeling lies in its ability to streamline the identification of threats, assess risks, and implement effective security measures early on, ultimately reducing costs and reinforcing compliance. With our intuitive threat modeling tool, users can quickly visualize components and communication flows, evaluate potential threats, and generate reports that demonstrate compliance, making security an integral part of their development process.
Frequently Asked Questions
RankInPublic FAQ
How does the tournament system work?
The tournament system on RankInPublic features daily matchups where new projects compete against each other. Community members vote for their favorites, and the winning product progresses to the next round, creating an engaging competitive atmosphere.
Can anyone submit a product?
Yes, RankInPublic welcomes submissions from all indie hackers and digital creators. Simply navigate to the launch section, submit your product, and you will be listed instantly on the platform.
What are the benefits of winning a tournament?
Winning a tournament on RankInPublic not only grants you the title of champion but also offers additional visibility through featured spotlights across the platform, enhancing your product's reach and credibility among potential users.
How can I participate in voting?
Participating in voting is straightforward. Simply create an account on RankInPublic, explore the ongoing tournaments, and cast your votes for the projects you support. Your engagement helps shape the visibility of innovative products in the ecosystem.
Threat Modeling FAQ
What is Threat Modeling?
Threat Modeling is a structured approach to identifying and addressing potential security threats in software design. It involves analyzing system architecture and workflows to proactively mitigate risks.
Who can benefit from using Threat Modeling?
Developers, security teams, and project managers can all benefit from Threat Modeling. It equips them with the tools and methodologies necessary to integrate security effectively into their development processes.
How does Threat Modeling improve security?
By identifying threats early in the design phase, Threat Modeling allows teams to implement security measures before vulnerabilities can be exploited. This proactive approach reduces the likelihood of costly breaches.
Is your threat modeling tool easy to use?
Yes! Our threat modeling tool is designed for ease of use, allowing teams to get started quickly. With intuitive interfaces and helpful resources, users can begin threat modeling within minutes, regardless of their experience level.
Alternatives
RankInPublic Alternatives
RankInPublic is an exciting platform tailored for indie hackers and digital creators, enabling them to showcase their innovative products in a competitive, tournament-style format. This dynamic environment allows users to engage with new projects daily, casting votes for their favorites while uncovering the latest tools in the tech ecosystem. The platform stands out by providing essential visibility to early-stage startups, facilitating organic engagement and community-driven feedback. Users often seek alternatives to RankInPublic for various reasons, including pricing considerations, specific feature sets, or compatibility with their platform needs. When searching for an alternative, it's crucial to consider factors such as user engagement dynamics, the size of the community, and the types of products typically featured. A good alternative should provide a supportive environment that fosters innovation and visibility for creators while aligning with your specific goals and preferences.
Threat Modeling Alternatives
Threat Modeling is an essential practice in the realm of software development, focusing on identifying potential threats during the design phase. By integrating security from the outset, it allows teams to build robust defenses rather than adding security as an afterthought. As organizations strive for greater efficiency and protection, users often seek alternatives to traditional threat modeling due to factors such as pricing, feature sets, and specific platform compatibility. The quest for a suitable alternative may hinge on ease of use, integration capabilities, and the ability to adapt to a team's unique workflow. When searching for an alternative to Threat Modeling, it's crucial to consider not only the pricing structures but also the range of features offered. Look for solutions that prioritize proactive security measures and provide seamless integration into existing processes. Additionally, evaluate user feedback and support options to ensure you choose a solution that aligns with your team’s needs and enhances overall security without compromising productivity.
