Threat Modeling
Empower your security strategy with our easy-to-use threat modeling tool for structured assessments and design.

About Threat Modeling
Threat Modeling is a proactive approach in cybersecurity that focuses on identifying, understanding, and mitigating potential threats during the design phase of software development. By integrating security into the development lifecycle, organizations can prevent vulnerabilities from being introduced, thereby adopting a "security by design" philosophy. This tool is designed for developers, security teams, and organizations aiming to enhance their security posture without compromising agility. The main value proposition of Threat Modeling lies in its ability to streamline the identification of threats, assess risks, and implement effective security measures early on, ultimately reducing costs and reinforcing compliance. With our intuitive threat modeling tool, users can quickly visualize components and communication flows, evaluate potential threats, and generate reports that demonstrate compliance, making security an integral part of their development process.
Features of Threat Modeling
Powerful Assessment Engine
Our powerful assessment engine allows users to understand potential threats and security weaknesses effectively. It evaluates the system architecture, identifies vulnerabilities, and helps prioritize risks based on their impact and likelihood, ensuring that organizations can focus on what matters most.
Flexible Diagram Engine
The flexible diagram engine enables users to visualize components and communication flows seamlessly. This feature aids in representing complex systems intuitively, allowing teams to collaborate and communicate effectively about security concerns and design choices.
Clear Reporting and Metrics
Our tool provides clear reporting and metrics that are essential for compliance demonstration. Users can generate detailed reports that outline identified threats, mitigations, and risk assessments, helping organizations maintain transparency and accountability in their security practices.
Extensive Resource Library
We offer a comprehensive resource library filled with articles, templates, and real-world examples to support users in their threat modeling journey. This library is designed to educate teams on various threat modeling methods, ensuring that they are well-equipped to tackle security challenges efficiently.
Use Cases of Threat Modeling
Early Detection of Vulnerabilities
By employing threat modeling during the design phase, teams can identify and address vulnerabilities before they escalate into costly security incidents. This proactive approach minimizes risk and reinforces security from the outset.
Streamlining Compliance Efforts
Organizations can use Threat Modeling to demonstrate compliance with industry standards and regulations more effectively. The tool's reporting features provide the documentation needed to showcase security efforts to stakeholders and regulatory bodies.
Enhancing Collaboration Among Teams
Threat Modeling fosters collaboration between development and security teams by providing a common framework for discussing threats and mitigation strategies. This shared understanding enhances communication and aligns security objectives with business goals.
Integrating Security into DevOps Processes
With the rise of DevOps practices, integrating threat modeling into the continuous integration and continuous deployment (CI/CD) pipeline ensures that security remains a priority throughout the software development lifecycle, rather than an afterthought.
Frequently Asked Questions
What is Threat Modeling?
Threat Modeling is a structured approach to identifying and addressing potential security threats in software design. It involves analyzing system architecture and workflows to proactively mitigate risks.
Who can benefit from using Threat Modeling?
Developers, security teams, and project managers can all benefit from Threat Modeling. It equips them with the tools and methodologies necessary to integrate security effectively into their development processes.
How does Threat Modeling improve security?
By identifying threats early in the design phase, Threat Modeling allows teams to implement security measures before vulnerabilities can be exploited. This proactive approach reduces the likelihood of costly breaches.
Is your threat modeling tool easy to use?
Yes! Our threat modeling tool is designed for ease of use, allowing teams to get started quickly. With intuitive interfaces and helpful resources, users can begin threat modeling within minutes, regardless of their experience level.
Top Alternatives to Threat Modeling
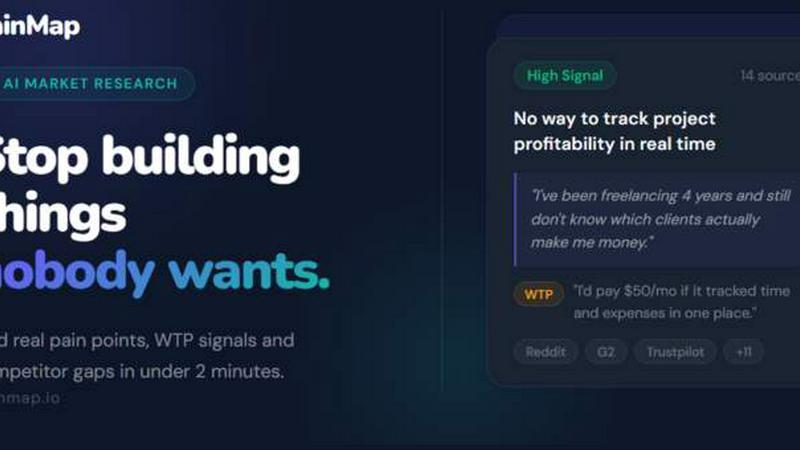
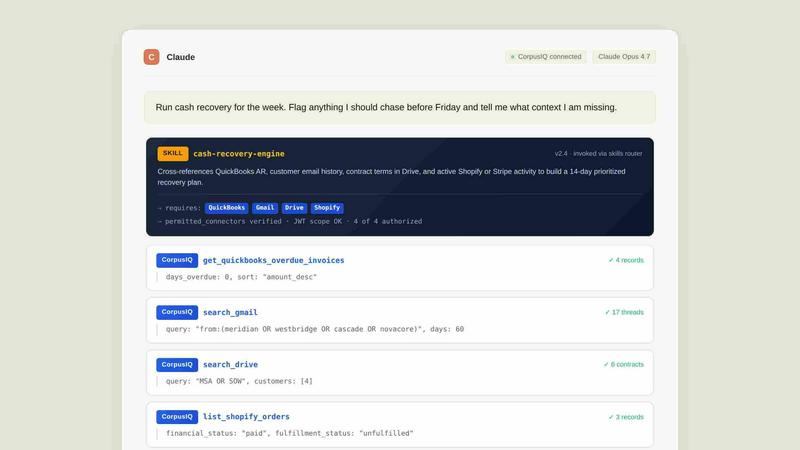
CorpusIQ
CorpusIQ connects your 43+ business tools to AI, delivering cited answers from 250+ skills in one private acceleration layer.
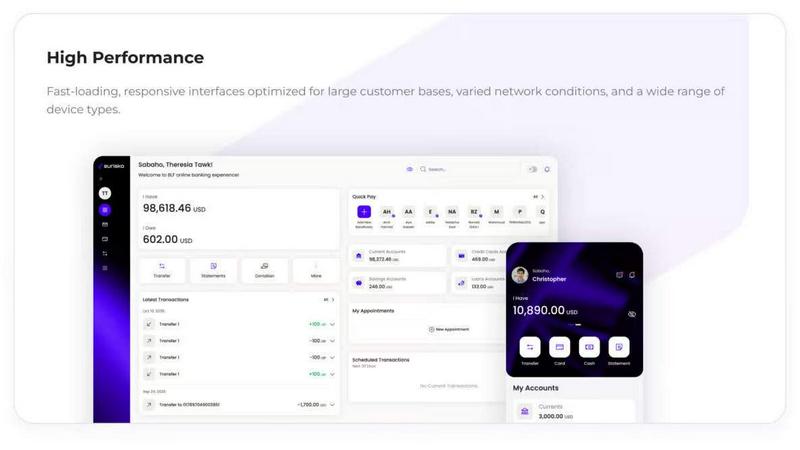
Eurisko Digital Banking Platform
Eurisko Digital Banking Platform lets you launch AI-powered banking journeys 4x faster with full control and zero vendor lock-in.
LoginRadius
LoginRadius is an API-first IAM platform delivering enterprise-grade authentication and user management for growing B2B and CIAM apps.
Helpyly
Helpyly is a centralized support hub that automates ticket management and workflows to help your team resolve issues faster.
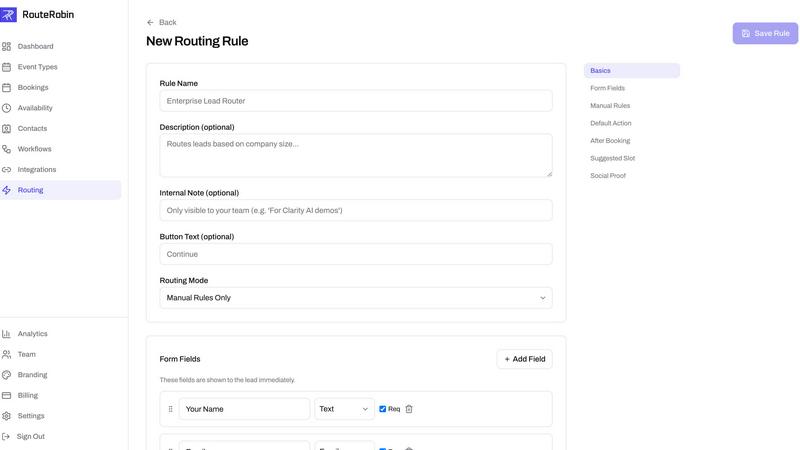
RouteRobin
RouteRobin uses AI to capture, qualify, and route leads to the right rep, transforming them into booked meetings effortlessly.