RedVeil vs Threat Modeling
Last updated: February 28, 2026
Last updated: February 28, 2026
Visual Comparison
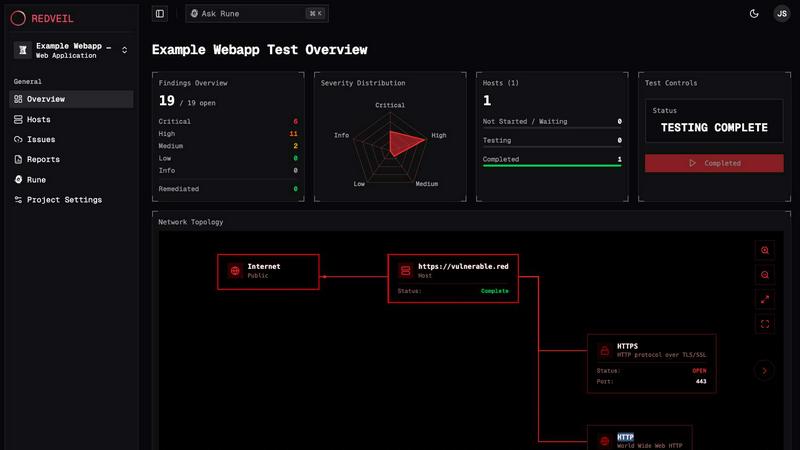
RedVeil
Threat Modeling

Feature Comparison
RedVeil
Speed & Efficiency
RedVeil dramatically shortens the pentesting timeline, allowing you to initiate tests within minutes rather than waiting weeks. This rapid deployment means you can receive security insights almost immediately, making it an ideal solution for teams operating in agile environments.
AI-Driven Insights
The platform utilizes intelligent AI agents that simulate real-world attack scenarios, identifying not just vulnerabilities but also exploit paths. Each finding comes with detailed context, reproduction steps, and remediation guidance, ensuring that you understand the implications of each vulnerability.
Compliance-Ready Reporting
RedVeil generates professional, audit-ready reports with just one click. These reports are tailored for various compliance frameworks, including SOC 2, ISO 27001, and PCI-DSS, ensuring you can easily meet regulatory requirements without additional effort.
Flexible Scheduling
With RedVeil, you have complete control over your testing schedule. Whether you need regular assessments or on-demand testing following a major deployment, you can easily allocate and schedule tests according to your needs, removing the headaches of traditional pentesting processes.
Threat Modeling
Powerful Assessment Engine
Our powerful assessment engine allows users to understand potential threats and security weaknesses effectively. It evaluates the system architecture, identifies vulnerabilities, and helps prioritize risks based on their impact and likelihood, ensuring that organizations can focus on what matters most.
Flexible Diagram Engine
The flexible diagram engine enables users to visualize components and communication flows seamlessly. This feature aids in representing complex systems intuitively, allowing teams to collaborate and communicate effectively about security concerns and design choices.
Clear Reporting and Metrics
Our tool provides clear reporting and metrics that are essential for compliance demonstration. Users can generate detailed reports that outline identified threats, mitigations, and risk assessments, helping organizations maintain transparency and accountability in their security practices.
Extensive Resource Library
We offer a comprehensive resource library filled with articles, templates, and real-world examples to support users in their threat modeling journey. This library is designed to educate teams on various threat modeling methods, ensuring that they are well-equipped to tackle security challenges efficiently.
Use Cases
RedVeil
Continuous Security Assessment
For organizations that deploy code frequently, RedVeil provides a continuous security assessment model. You can run penetration tests whenever your environment changes, ensuring that new vulnerabilities are identified and addressed immediately.
Compliance Preparation
Companies preparing for compliance audits can leverage RedVeil to generate necessary reports quickly. The platform's ability to produce audit-ready documentation ensures that you can meet compliance deadlines with confidence and ease.
Vulnerability Remediation
After identifying vulnerabilities, RedVeil's guided remediation features allow teams to understand what went wrong and how to fix it. This makes it easier for your engineering team to implement security patches and improve your security posture effectively.
Risk Management
RedVeil helps organizations assess their risk by identifying real, exploitable vulnerabilities. By understanding the potential impact of these risks, business leaders can prioritize security investments and allocate resources more effectively.
Threat Modeling
Early Detection of Vulnerabilities
By employing threat modeling during the design phase, teams can identify and address vulnerabilities before they escalate into costly security incidents. This proactive approach minimizes risk and reinforces security from the outset.
Streamlining Compliance Efforts
Organizations can use Threat Modeling to demonstrate compliance with industry standards and regulations more effectively. The tool's reporting features provide the documentation needed to showcase security efforts to stakeholders and regulatory bodies.
Enhancing Collaboration Among Teams
Threat Modeling fosters collaboration between development and security teams by providing a common framework for discussing threats and mitigation strategies. This shared understanding enhances communication and aligns security objectives with business goals.
Integrating Security into DevOps Processes
With the rise of DevOps practices, integrating threat modeling into the continuous integration and continuous deployment (CI/CD) pipeline ensures that security remains a priority throughout the software development lifecycle, rather than an afterthought.
Overview
About RedVeil
RedVeil is a groundbreaking AI-powered penetration testing platform designed to meet the fast-paced demands of modern software development. Traditional pentesting methods often take weeks and result in a costly one-time snapshot of your security posture. In contrast, RedVeil enables organizations to conduct comprehensive, autonomous penetration tests in mere minutes, providing actionable, audit-ready reports by the afternoon. This solution is perfect for engineering teams that deploy code daily and need real-time insights into their security vulnerabilities. With RedVeil, you get the human-like reasoning of an expert hacker combined with the rapid execution capabilities of advanced software, ensuring that your security assessments keep pace with your development cycles. This innovative tool not only enhances your security posture but also streamlines compliance with industry standards, making it an essential asset for any organization serious about safeguarding its digital assets.
About Threat Modeling
Threat Modeling is a proactive approach in cybersecurity that focuses on identifying, understanding, and mitigating potential threats during the design phase of software development. By integrating security into the development lifecycle, organizations can prevent vulnerabilities from being introduced, thereby adopting a "security by design" philosophy. This tool is designed for developers, security teams, and organizations aiming to enhance their security posture without compromising agility. The main value proposition of Threat Modeling lies in its ability to streamline the identification of threats, assess risks, and implement effective security measures early on, ultimately reducing costs and reinforcing compliance. With our intuitive threat modeling tool, users can quickly visualize components and communication flows, evaluate potential threats, and generate reports that demonstrate compliance, making security an integral part of their development process.
Frequently Asked Questions
RedVeil FAQ
Does RedVeil perform a real penetration test?
Yes, RedVeil conducts real penetration tests using AI-driven agents that simulate human-like attack scenarios to discover and exploit vulnerabilities in your environment.
How many penetration tests can I do with my annual subscription?
The number of penetration tests you can perform depends on your subscription tier. For example, the Perimeter plan allows for 500 Agent Ops annually, while the Full Coverage plan offers 2,500 Agent Ops.
Is there a chance that my web application or network could go down during the test?
RedVeil is designed to minimize risk during testing. While no test is entirely risk-free, the platform implements best practices to mitigate the chances of downtime or disruption.
Can I use RedVeil's penetration test reports to meet the requirements of my compliance?
Absolutely! RedVeil generates compliance-ready reports that align with various standards, such as SOC 2, ISO 27001, and PCI-DSS, making it easy for you to demonstrate compliance to auditors.
Threat Modeling FAQ
What is Threat Modeling?
Threat Modeling is a structured approach to identifying and addressing potential security threats in software design. It involves analyzing system architecture and workflows to proactively mitigate risks.
Who can benefit from using Threat Modeling?
Developers, security teams, and project managers can all benefit from Threat Modeling. It equips them with the tools and methodologies necessary to integrate security effectively into their development processes.
How does Threat Modeling improve security?
By identifying threats early in the design phase, Threat Modeling allows teams to implement security measures before vulnerabilities can be exploited. This proactive approach reduces the likelihood of costly breaches.
Is your threat modeling tool easy to use?
Yes! Our threat modeling tool is designed for ease of use, allowing teams to get started quickly. With intuitive interfaces and helpful resources, users can begin threat modeling within minutes, regardless of their experience level.
Alternatives
RedVeil Alternatives
RedVeil is a cutting-edge software solution that revolutionizes penetration testing by combining the analytical reasoning of human hackers with the rapid execution capabilities of AI. It falls under the category of AI-driven cybersecurity tools, specifically designed to cater to the fast-paced demands of modern engineering teams that deploy code daily. As organizations increasingly seek agile and efficient security measures, many users find themselves exploring alternatives to traditional pentesting methods due to factors such as high costs, lengthy turnaround times, and limited flexibility in scheduling tests. When searching for alternatives to RedVeil, it's essential to consider various aspects such as pricing, feature sets, and compatibility with existing platforms. Users should look for solutions that not only offer competitive pricing and comprehensive testing capabilities but also provide the flexibility to meet their unique operational needs. Additionally, the ability to generate audit-ready reports swiftly is a crucial factor to consider, ensuring that any chosen solution aligns with the organization's compliance requirements and enhances overall security posture.
Threat Modeling Alternatives
Threat Modeling is an essential practice in the realm of software development, focusing on identifying potential threats during the design phase. By integrating security from the outset, it allows teams to build robust defenses rather than adding security as an afterthought. As organizations strive for greater efficiency and protection, users often seek alternatives to traditional threat modeling due to factors such as pricing, feature sets, and specific platform compatibility. The quest for a suitable alternative may hinge on ease of use, integration capabilities, and the ability to adapt to a team's unique workflow. When searching for an alternative to Threat Modeling, it's crucial to consider not only the pricing structures but also the range of features offered. Look for solutions that prioritize proactive security measures and provide seamless integration into existing processes. Additionally, evaluate user feedback and support options to ensure you choose a solution that aligns with your team’s needs and enhances overall security without compromising productivity.
