Appkittie vs Threat Modeling
Appkittie
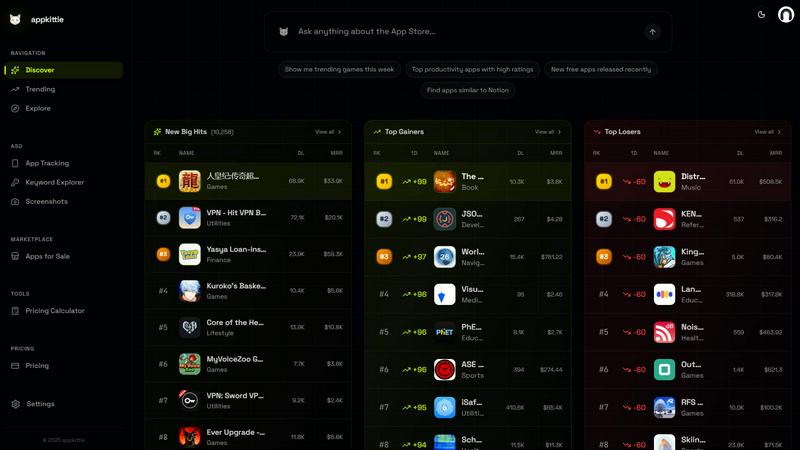
Unlock app success by replicating proven winners, tracking top ads, and discovering lucrative keywords with Appkittie.
Last updated: March 18, 2026
Last updated: February 28, 2026
Visual Comparison
Appkittie
Threat Modeling

Feature Comparison
Appkittie
App Discovery & Filtering Engine
The App Discovery & Filtering Engine allows users to seamlessly explore a vast array of mobile apps. With advanced filtering options, you can access crucial revenue and download data, helping you identify high-income apps and spot emerging trends in various markets.
Winning Ads Spy
With the Winning Ads Spy feature, you can visualize current Meta ads and discover compelling ad creatives that are driving success. This powerful tool enables you to invest in advertisements that are proven to work, ensuring your marketing budget is utilized effectively.
Creator & Influencer Tracker
The Creator & Influencer Tracker is designed to help you uncover the user-generated content (UGC) creators behind successful apps. By identifying their influencer campaigns, you can pinpoint viral growth drivers and leverage their strategies to enhance your app's visibility.
Keyword & ASO Intelligence
Maximize your app's exposure with the Keyword & ASO Intelligence feature. This tool helps you discover high-traffic keywords tailored to your app's niche and provides personalized ASO suggestions, allowing you to outrank competitors and improve your app's searchability.
Threat Modeling
Powerful Assessment Engine
Our powerful assessment engine allows users to understand potential threats and security weaknesses effectively. It evaluates the system architecture, identifies vulnerabilities, and helps prioritize risks based on their impact and likelihood, ensuring that organizations can focus on what matters most.
Flexible Diagram Engine
The flexible diagram engine enables users to visualize components and communication flows seamlessly. This feature aids in representing complex systems intuitively, allowing teams to collaborate and communicate effectively about security concerns and design choices.
Clear Reporting and Metrics
Our tool provides clear reporting and metrics that are essential for compliance demonstration. Users can generate detailed reports that outline identified threats, mitigations, and risk assessments, helping organizations maintain transparency and accountability in their security practices.
Extensive Resource Library
We offer a comprehensive resource library filled with articles, templates, and real-world examples to support users in their threat modeling journey. This library is designed to educate teams on various threat modeling methods, ensuring that they are well-equipped to tackle security challenges efficiently.
Use Cases
Appkittie
Finding Your Next Startup Idea
If you're an entrepreneur seeking your next big idea, Appkittie can help you identify validated app concepts that are already thriving in the market. By analyzing proven app metrics, you can focus your efforts on building something that has real demand.
Validating a Niche
For indie hackers looking to penetrate a specific niche, Appkittie provides the insights needed to validate your ideas. With data on existing apps in that space, you can assess their performance and determine if there's an opportunity worth pursuing.
Competitor Research
Conducting competitor analysis has never been easier. Appkittie lets you track and analyze competitors' successful apps, marketing strategies, and user acquisition tactics, enabling you to learn from their successes and avoid their pitfalls.
Enhancing App Store Optimization (ASO)
Appkittie's ASO tools are vital for developers aiming to improve their app's visibility. By utilizing high-traffic keywords and optimizing your app store metadata accordingly, you can boost downloads and enhance your app's position in search results.
Threat Modeling
Early Detection of Vulnerabilities
By employing threat modeling during the design phase, teams can identify and address vulnerabilities before they escalate into costly security incidents. This proactive approach minimizes risk and reinforces security from the outset.
Streamlining Compliance Efforts
Organizations can use Threat Modeling to demonstrate compliance with industry standards and regulations more effectively. The tool's reporting features provide the documentation needed to showcase security efforts to stakeholders and regulatory bodies.
Enhancing Collaboration Among Teams
Threat Modeling fosters collaboration between development and security teams by providing a common framework for discussing threats and mitigation strategies. This shared understanding enhances communication and aligns security objectives with business goals.
Integrating Security into DevOps Processes
With the rise of DevOps practices, integrating threat modeling into the continuous integration and continuous deployment (CI/CD) pipeline ensures that security remains a priority throughout the software development lifecycle, rather than an afterthought.
Overview
About Appkittie
Appkittie is a revolutionary app intelligence platform tailored for founders, indie hackers, and marketers eager to discover viable app opportunities without the guesswork. By analyzing a rich database of mobile applications, Appkittie reveals which apps are generating substantial revenue and downloads, empowering users to make informed decisions. Its advanced analytics extend beyond mere numbers; the platform unveils the marketing strategies that successful apps employ. Users can explore winning advertisements, identify influential creators on platforms like TikTok, and dissect Apple Search Ads campaigns. This insight equips users to replicate proven growth strategies, saving valuable time and resources while steering clear of ideas lacking traction. Whether you're hunting for your next startup idea, validating a niche, or conducting competitor research, Appkittie provides the essential insights needed to build apps that resonate with real market demand.
About Threat Modeling
Threat Modeling is a proactive approach in cybersecurity that focuses on identifying, understanding, and mitigating potential threats during the design phase of software development. By integrating security into the development lifecycle, organizations can prevent vulnerabilities from being introduced, thereby adopting a "security by design" philosophy. This tool is designed for developers, security teams, and organizations aiming to enhance their security posture without compromising agility. The main value proposition of Threat Modeling lies in its ability to streamline the identification of threats, assess risks, and implement effective security measures early on, ultimately reducing costs and reinforcing compliance. With our intuitive threat modeling tool, users can quickly visualize components and communication flows, evaluate potential threats, and generate reports that demonstrate compliance, making security an integral part of their development process.
Frequently Asked Questions
Appkittie FAQ
What can I actually do with Appkittie?
With Appkittie, you can discover profitable app opportunities, analyze competitors, track winning ads, uncover high-traffic keywords, and generate app store screenshots, all designed to help you build successful apps.
Who is Appkittie built for?
Appkittie is tailored for founders, indie hackers, marketers, and anyone interested in app development. It's a perfect tool for those looking to uncover insights that lead to successful app launches and growth strategies.
What data and markets does Appkittie cover today?
Appkittie covers a wide range of mobile app data, including revenue, downloads, marketing strategies, and keyword performance across various global markets. This extensive coverage allows users to make informed decisions based on comprehensive data.
Is there a free trial, and can I cancel anytime?
Yes, Appkittie offers a 3-day free trial that allows you to explore its features without any upfront charges. You can cancel anytime during the trial period, ensuring that you have the flexibility to evaluate the platform thoroughly.
Threat Modeling FAQ
What is Threat Modeling?
Threat Modeling is a structured approach to identifying and addressing potential security threats in software design. It involves analyzing system architecture and workflows to proactively mitigate risks.
Who can benefit from using Threat Modeling?
Developers, security teams, and project managers can all benefit from Threat Modeling. It equips them with the tools and methodologies necessary to integrate security effectively into their development processes.
How does Threat Modeling improve security?
By identifying threats early in the design phase, Threat Modeling allows teams to implement security measures before vulnerabilities can be exploited. This proactive approach reduces the likelihood of costly breaches.
Is your threat modeling tool easy to use?
Yes! Our threat modeling tool is designed for ease of use, allowing teams to get started quickly. With intuitive interfaces and helpful resources, users can begin threat modeling within minutes, regardless of their experience level.
Alternatives
Appkittie Alternatives
Appkittie is an innovative app intelligence platform designed specifically for founders, indie hackers, and marketers seeking to uncover successful app opportunities in the competitive mobile landscape. By analyzing extensive data on mobile applications, Appkittie empowers users to make informed decisions on what to build and how to market it effectively. Users often search for alternatives to Appkittie due to various reasons, such as pricing, specific feature sets, or compatibility with different platforms. When choosing an alternative, it’s essential to consider factors like ease of use, the depth of analytics provided, and the level of support available. These criteria will help you select a platform that aligns well with your goals and enhances your ability to identify viable app opportunities.
Threat Modeling Alternatives
Threat Modeling is an essential practice in the realm of software development, focusing on identifying potential threats during the design phase. By integrating security from the outset, it allows teams to build robust defenses rather than adding security as an afterthought. As organizations strive for greater efficiency and protection, users often seek alternatives to traditional threat modeling due to factors such as pricing, feature sets, and specific platform compatibility. The quest for a suitable alternative may hinge on ease of use, integration capabilities, and the ability to adapt to a team's unique workflow. When searching for an alternative to Threat Modeling, it's crucial to consider not only the pricing structures but also the range of features offered. Look for solutions that prioritize proactive security measures and provide seamless integration into existing processes. Additionally, evaluate user feedback and support options to ensure you choose a solution that aligns with your team’s needs and enhances overall security without compromising productivity.
