Browsable vs Threat Modeling
Browsable
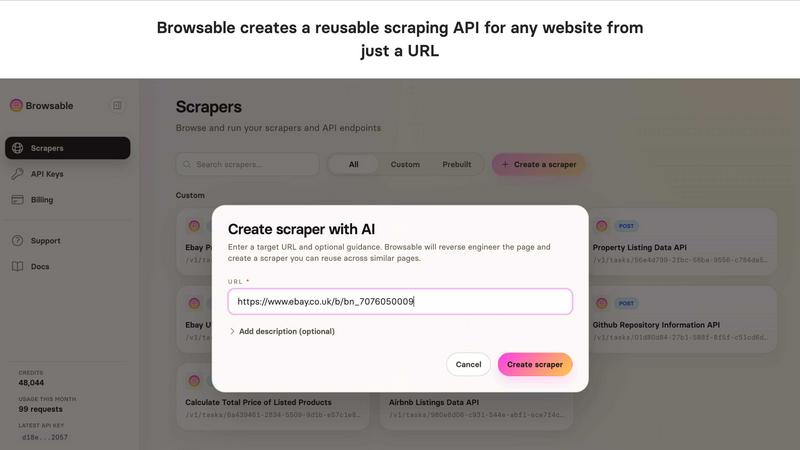
Browsable instantly turns any website into a clean, structured API for easy data extraction without coding.
Last updated: March 18, 2026
Last updated: February 28, 2026
Visual Comparison
Browsable
Threat Modeling

Feature Comparison
Browsable
AI-Powered API Generation
Simply provide a target URL, and Browsable's AI agent takes over. It doesn't just scrape; it intelligently analyzes the page layout, identifies key data points (like product titles, prices, reviews), and reverse-engineers the underlying structure to build a robust, parameterized API endpoint. This process automates the weeks of manual work typically required to build a reliable web scraper, delivering a production-ready API in minutes that can be reused across thousands of similar pages.
Pre-Built Scrapers for Major Platforms
Jumpstart your projects with our growing library of pre-built, maintained APIs for the world's most popular websites. Need data from Airbnb, Amazon, Instagram, or Reddit? These scrapers are available immediately, offering normalized data schemas and reliable uptime. We continuously update these scrapers to combat site changes and anti-bot measures, saving you from the constant maintenance burden of do-it-yourself scraping scripts.
No-Code Dashboard & Data Export
You don't need to be a developer to harness the power of Browsable. Use the intuitive web dashboard to run scraping tasks on-demand. Configure your parameters, execute the scrape, and instantly download the clean, structured results as a CSV or JSON file. This makes Browsable perfect for business analysts, marketers, and researchers who need to gather data quickly for reports, spreadsheets, or further analysis without writing a single line of code.
Advanced Anti-Block Technology
Websites actively fight scrapers with evolving defenses. Browsable is built to win this battle. Our system employs a sophisticated combination of residential proxies, realistic browser fingerprinting, smart request throttling, and automatic retry logic. This multi-layered approach ensures your scraping requests succeed where others fail, providing reliable data access even against the most aggressive anti-bot systems like Cloudflare, without you managing the technical complexity.
Threat Modeling
Powerful Assessment Engine
Our powerful assessment engine allows users to understand potential threats and security weaknesses effectively. It evaluates the system architecture, identifies vulnerabilities, and helps prioritize risks based on their impact and likelihood, ensuring that organizations can focus on what matters most.
Flexible Diagram Engine
The flexible diagram engine enables users to visualize components and communication flows seamlessly. This feature aids in representing complex systems intuitively, allowing teams to collaborate and communicate effectively about security concerns and design choices.
Clear Reporting and Metrics
Our tool provides clear reporting and metrics that are essential for compliance demonstration. Users can generate detailed reports that outline identified threats, mitigations, and risk assessments, helping organizations maintain transparency and accountability in their security practices.
Extensive Resource Library
We offer a comprehensive resource library filled with articles, templates, and real-world examples to support users in their threat modeling journey. This library is designed to educate teams on various threat modeling methods, ensuring that they are well-equipped to tackle security challenges efficiently.
Use Cases
Browsable
Competitive Intelligence & Price Monitoring
Track competitor pricing, product assortments, and promotional strategies in real-time. Automatically scrape e-commerce sites like Amazon, eBay, or Walmart to monitor price fluctuations, stock availability, and customer reviews. Feed this structured data into your dashboards to dynamically adjust your own pricing strategy and stay ahead in the market without manual, error-prone checks.
Market Research & Lead Generation
Aggregate public data to build rich prospect lists and market analyses. Scrape business directories, professional networks like LinkedIn, real estate listings, or job boards to gather company details, contact information, and key insights. Transform scattered web information into a structured database for your sales, recruiting, or investment teams to act upon efficiently.
Content Aggregation & AI Training
Build custom datasets to train or fuel AI models and applications. Scrape news articles, social media posts, forum discussions, or video metadata from platforms like YouTube and Reddit to create tailored datasets for sentiment analysis, trend forecasting, or content recommendation engines. Browsable turns the web into your vast, customizable data lake.
Business Process Automation
Integrate web data directly into your internal tools and workflows. Automatically pull shipping statuses, supplier inventory levels, review ratings, or local event listings into your CRM, ERP, or custom software via API. Eliminate manual data entry, reduce errors, and keep your systems synchronized with the latest information from the web.
Threat Modeling
Early Detection of Vulnerabilities
By employing threat modeling during the design phase, teams can identify and address vulnerabilities before they escalate into costly security incidents. This proactive approach minimizes risk and reinforces security from the outset.
Streamlining Compliance Efforts
Organizations can use Threat Modeling to demonstrate compliance with industry standards and regulations more effectively. The tool's reporting features provide the documentation needed to showcase security efforts to stakeholders and regulatory bodies.
Enhancing Collaboration Among Teams
Threat Modeling fosters collaboration between development and security teams by providing a common framework for discussing threats and mitigation strategies. This shared understanding enhances communication and aligns security objectives with business goals.
Integrating Security into DevOps Processes
With the rise of DevOps practices, integrating threat modeling into the continuous integration and continuous deployment (CI/CD) pipeline ensures that security remains a priority throughout the software development lifecycle, rather than an afterthought.
Overview
About Browsable
Browsable is the revolutionary AI web scraper that instantly transforms any website into a powerful, reusable API. It solves the fundamental problem of data accessibility on the modern web: valuable information is locked away in HTML, with no official API in sight. Browsable changes the game by using intelligent agents to analyze a webpage you provide, automatically determine what data can be extracted, and reverse-engineer the site's structure to generate a fully functional scraping API on the fly. This isn't a one-time scrape; the generated API works for any page with the same structure, making it a permanent, scalable solution for data integration.
Built for developers, data scientists, businesses, and AI agents, Browsable democratizes access to web data. Whether you're building an application that needs live pricing, conducting market research, training AI models, or simply need to export data for analysis, Browsable removes the technical headache. It handles the complexities of modern web scraping—like dynamic JavaScript content, logins, pagination, and aggressive anti-bot protections—so you don't have to. With features like pre-built APIs for popular sites and a no-code dashboard for instant CSV/JSON downloads, Browsable is the all-in-one platform to unlock the web's data, turning static websites into dynamic, structured data streams with just a URL.
About Threat Modeling
Threat Modeling is a proactive approach in cybersecurity that focuses on identifying, understanding, and mitigating potential threats during the design phase of software development. By integrating security into the development lifecycle, organizations can prevent vulnerabilities from being introduced, thereby adopting a "security by design" philosophy. This tool is designed for developers, security teams, and organizations aiming to enhance their security posture without compromising agility. The main value proposition of Threat Modeling lies in its ability to streamline the identification of threats, assess risks, and implement effective security measures early on, ultimately reducing costs and reinforcing compliance. With our intuitive threat modeling tool, users can quickly visualize components and communication flows, evaluate potential threats, and generate reports that demonstrate compliance, making security an integral part of their development process.
Frequently Asked Questions
Browsable FAQ
How does Browsable handle websites with login requirements?
Browsable can manage authenticated scraping sessions. When generating your scraper, you can configure it to handle logins by providing credentials or session cookies through the secure dashboard or API parameters. Our system automates the login process and maintains the session to access gated content, just like a real user would, ensuring you can scrape data from private accounts or member-only areas.
What happens if a website changes its layout and breaks my scraper?
This is a core problem Browsable is designed to solve. For our pre-built APIs, our team actively monitors for site changes and updates the scrapers to maintain compatibility. For custom AI-generated scrapers, our system includes monitoring and alerting. If a scraper begins to fail due to layout changes, you are notified and can easily re-run the AI analysis on the updated page to regenerate a working API endpoint, minimizing downtime.
Is web scraping with Browsable legal?
Browsable provides a powerful tool for accessing publicly available data. It is your responsibility to use it ethically and in compliance with applicable laws, a website's Terms of Service, and robots.txt files. We strongly advise users to respect copyright, avoid overloading servers, and not scrape personal data without consent. Always consult legal counsel if you are unsure about the legality of your specific use case.
Can I scrape large volumes of data or schedule recurring scrapes?
Absolutely. Browsable is built for scale. You can configure scrapers to handle pagination and extract data from thousands of pages. Through our API, you can integrate scraping tasks into your scheduled workflows (e.g., using cron jobs). Our paid plans offer higher credit limits and concurrency to support large-scale, automated data extraction pipelines for enterprise needs.
Threat Modeling FAQ
What is Threat Modeling?
Threat Modeling is a structured approach to identifying and addressing potential security threats in software design. It involves analyzing system architecture and workflows to proactively mitigate risks.
Who can benefit from using Threat Modeling?
Developers, security teams, and project managers can all benefit from Threat Modeling. It equips them with the tools and methodologies necessary to integrate security effectively into their development processes.
How does Threat Modeling improve security?
By identifying threats early in the design phase, Threat Modeling allows teams to implement security measures before vulnerabilities can be exploited. This proactive approach reduces the likelihood of costly breaches.
Is your threat modeling tool easy to use?
Yes! Our threat modeling tool is designed for ease of use, allowing teams to get started quickly. With intuitive interfaces and helpful resources, users can begin threat modeling within minutes, regardless of their experience level.
Alternatives
Browsable Alternatives
Browsable is an AI-powered web scraping API that instantly turns any webpage into a reusable data pipeline. It belongs to the category of data extraction and automation tools, designed to unlock the vast amounts of public data trapped inside websites without official APIs. It's the fast track from a URL to structured, usable data. Users often explore alternatives for various reasons, such as budget constraints, specific feature requirements like proxy rotation or CAPTCHA handling, or the need for a different platform like a desktop application versus a cloud API. The landscape offers many tools, each with its own strengths and focus. When choosing an alternative, key considerations include the learning curve, scalability for large projects, reliability against anti-bot measures, and the format of the output data. It's crucial to find a solution that balances power with ease of use, fitting seamlessly into your specific workflow and technical stack.
Threat Modeling Alternatives
Threat Modeling is an essential practice in the realm of software development, focusing on identifying potential threats during the design phase. By integrating security from the outset, it allows teams to build robust defenses rather than adding security as an afterthought. As organizations strive for greater efficiency and protection, users often seek alternatives to traditional threat modeling due to factors such as pricing, feature sets, and specific platform compatibility. The quest for a suitable alternative may hinge on ease of use, integration capabilities, and the ability to adapt to a team's unique workflow. When searching for an alternative to Threat Modeling, it's crucial to consider not only the pricing structures but also the range of features offered. Look for solutions that prioritize proactive security measures and provide seamless integration into existing processes. Additionally, evaluate user feedback and support options to ensure you choose a solution that aligns with your team’s needs and enhances overall security without compromising productivity.
