Threat Modeling vs Vector
Last updated: February 28, 2026
Last updated: April 13, 2026
Visual Comparison
Threat Modeling

Vector
Feature Comparison
Threat Modeling
Powerful Assessment Engine
Our powerful assessment engine allows users to understand potential threats and security weaknesses effectively. It evaluates the system architecture, identifies vulnerabilities, and helps prioritize risks based on their impact and likelihood, ensuring that organizations can focus on what matters most.
Flexible Diagram Engine
The flexible diagram engine enables users to visualize components and communication flows seamlessly. This feature aids in representing complex systems intuitively, allowing teams to collaborate and communicate effectively about security concerns and design choices.
Clear Reporting and Metrics
Our tool provides clear reporting and metrics that are essential for compliance demonstration. Users can generate detailed reports that outline identified threats, mitigations, and risk assessments, helping organizations maintain transparency and accountability in their security practices.
Extensive Resource Library
We offer a comprehensive resource library filled with articles, templates, and real-world examples to support users in their threat modeling journey. This library is designed to educate teams on various threat modeling methods, ensuring that they are well-equipped to tackle security challenges efficiently.
Vector
AI Everything
Intelligence is baked into the core of the Vector platform, automating complex tasks and providing smart insights to guide your decisions. This isn't just a chatbot add-on; it's a foundational layer that helps optimize your product, understand your customers, and streamline operations, allowing you to focus on strategy and growth instead of manual configuration and guesswork.
Built-in Authentication & Accounts
Get secure, professional-grade customer accounts out of the box. Vector handles the entire user identity flow, allowing your customers to easily sign up, log in, and manage their profiles. This critical infrastructure is set up instantly, saving you months of development time and security headaches, with no expensive engineer required to implement or maintain it.
Frictionless Payments with Stripe
Integrate powerful, global payments seamlessly without the typical pain. Vector provides a streamlined Stripe experience, enabling you to accept payments, manage subscriptions, and handle billing from within your dashboard. This feature removes the complexity of financial compliance and gateway setup, so you can start earning revenue immediately after launch.
One-Click Deployment & Infrastructure
Go from building to live on the internet with a single click. Vector manages all the complex cloud infrastructure, hosting, and deployment pipelines for you. This means no more wrestling with servers, domains, or SSL certificates. Your product is always secure, scalable, and instantly accessible to your customers worldwide, without any dev-ops expertise.
Use Cases
Threat Modeling
Early Detection of Vulnerabilities
By employing threat modeling during the design phase, teams can identify and address vulnerabilities before they escalate into costly security incidents. This proactive approach minimizes risk and reinforces security from the outset.
Streamlining Compliance Efforts
Organizations can use Threat Modeling to demonstrate compliance with industry standards and regulations more effectively. The tool's reporting features provide the documentation needed to showcase security efforts to stakeholders and regulatory bodies.
Enhancing Collaboration Among Teams
Threat Modeling fosters collaboration between development and security teams by providing a common framework for discussing threats and mitigation strategies. This shared understanding enhances communication and aligns security objectives with business goals.
Integrating Security into DevOps Processes
With the rise of DevOps practices, integrating threat modeling into the continuous integration and continuous deployment (CI/CD) pipeline ensures that security remains a priority throughout the software development lifecycle, rather than an afterthought.
Vector
Launching a SaaS Product
Turn your software idea into a live, subscription-based business in days, not months. Use Vector to build your application, integrate member-only areas with authentication, set up tiered pricing plans via Stripe, and deploy instantly. It's the perfect stack for solo founders to validate and scale a SaaS without a technical co-founder or large upfront investment.
Creating a Premium Content Hub
Monetize your expertise by building a gated community or premium content platform. Vector allows you to quickly create a site where users must sign up and pay for access to exclusive videos, articles, or forums. The built-in accounts and payments handle all the transactional complexity, letting you concentrate solely on creating value for your members.
Validating a New Business Idea
Rapidly test market demand with a functional, revenue-ready prototype. Instead of building a non-monetizable "throwaway" demo, use Vector to launch a minimal viable product (MVP) that can actually accept payments from day one. This allows for true validation with real customers and real money, providing concrete data to guide your next steps.
Scaling an Existing Side Project
Take your side hustle to the next level without rebuilding from scratch. If you have a project that's outgrowing its initial platform, Vector provides the professional infrastructure to scale. Migrate to handle increased traffic, implement proper customer accounts, introduce paid features, and manage growth—all from one centralized, powerful dashboard.
Overview
About Threat Modeling
Threat Modeling is a proactive approach in cybersecurity that focuses on identifying, understanding, and mitigating potential threats during the design phase of software development. By integrating security into the development lifecycle, organizations can prevent vulnerabilities from being introduced, thereby adopting a "security by design" philosophy. This tool is designed for developers, security teams, and organizations aiming to enhance their security posture without compromising agility. The main value proposition of Threat Modeling lies in its ability to streamline the identification of threats, assess risks, and implement effective security measures early on, ultimately reducing costs and reinforcing compliance. With our intuitive threat modeling tool, users can quickly visualize components and communication flows, evaluate potential threats, and generate reports that demonstrate compliance, making security an integral part of their development process.
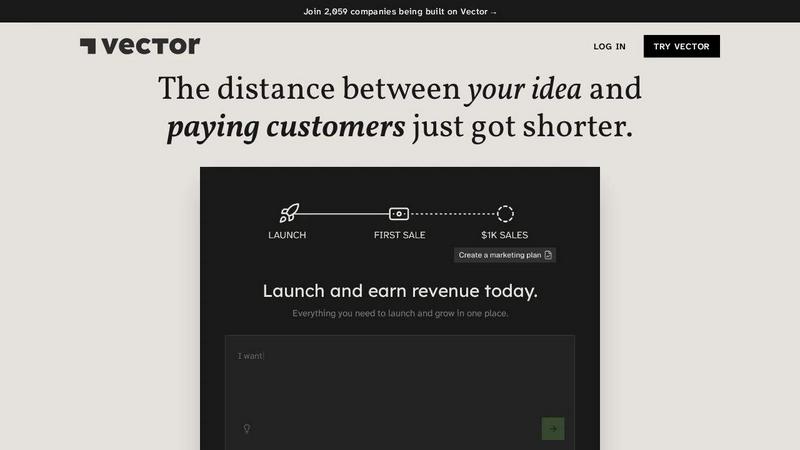
About Vector
Vector is the AI-powered launchpad for modern founders. It's the all-in-one platform that transforms your raw idea into a live, revenue-generating company in record time. Built for entrepreneurs, indie hackers, and creators, Vector eliminates the traditional barriers of starting a business: complex coding, expensive engineering hires, and fragmented tools. Its core value proposition is simple yet powerful: drastically shorten the distance between your idea and paying customers. From the initial concept through to marketing, payments, and scaling, Vector provides the integrated infrastructure and intelligent automation to build and run your entire business from a single, intuitive dashboard. With out-of-the-box features like authentication, one-click deployment, and Stripe integration, you can launch a professional, secure product today. Vector is more than just a builder; it's a growth engine designed to help you make money from day one, not just create throwaway prototypes. Start for free, keep 100% of your equity, and join thousands of others who are building the future on Vector.
Frequently Asked Questions
Threat Modeling FAQ
What is Threat Modeling?
Threat Modeling is a structured approach to identifying and addressing potential security threats in software design. It involves analyzing system architecture and workflows to proactively mitigate risks.
Who can benefit from using Threat Modeling?
Developers, security teams, and project managers can all benefit from Threat Modeling. It equips them with the tools and methodologies necessary to integrate security effectively into their development processes.
How does Threat Modeling improve security?
By identifying threats early in the design phase, Threat Modeling allows teams to implement security measures before vulnerabilities can be exploited. This proactive approach reduces the likelihood of costly breaches.
Is your threat modeling tool easy to use?
Yes! Our threat modeling tool is designed for ease of use, allowing teams to get started quickly. With intuitive interfaces and helpful resources, users can begin threat modeling within minutes, regardless of their experience level.
Vector FAQ
What makes Vector different from other AI app builders?
Vector is an all-in-one business platform, not just an app builder. While others focus on generating front-end code, Vector provides the entire backend business engine: live customer authentication, integrated payments (Stripe), one-click hosting, and built-in growth tools. It's designed explicitly to get you to revenue, helping you run and scale your entire company.
Does Vector help me manage customer accounts?
Absolutely. Professional customer account management is a core, out-of-the-box feature. From sign-up and login flows to secure session management and user profiles, Vector handles it all. You get a full dashboard to view and manage your customers without writing a single line of backend code or worrying about security best practices.
Do I need a credit card to try Vector?
No, you do not. Vector offers a free trial with no credit card required to start. You can explore the platform, begin building your product, and experience its core features without any financial commitment. This allows you to genuinely test its capabilities and see if it's the right fit for your venture before any payment is needed.
Do I retain ownership of my data and IP?
Yes, completely. You maintain 100% ownership of all your intellectual property, data, and customer information. Vector is a platform to build and host your business, not a partner that claims rights to your assets. Your ideas, your code, and your customer relationships remain solely and unequivocally yours.
Alternatives
Threat Modeling Alternatives
Threat Modeling is an essential practice in the realm of software development, focusing on identifying potential threats during the design phase. By integrating security from the outset, it allows teams to build robust defenses rather than adding security as an afterthought. As organizations strive for greater efficiency and protection, users often seek alternatives to traditional threat modeling due to factors such as pricing, feature sets, and specific platform compatibility. The quest for a suitable alternative may hinge on ease of use, integration capabilities, and the ability to adapt to a team's unique workflow. When searching for an alternative to Threat Modeling, it's crucial to consider not only the pricing structures but also the range of features offered. Look for solutions that prioritize proactive security measures and provide seamless integration into existing processes. Additionally, evaluate user feedback and support options to ensure you choose a solution that aligns with your team’s needs and enhances overall security without compromising productivity.
Vector Alternatives
Vector is an AI-powered software platform designed to help entrepreneurs and innovators turn their ideas into fully operational companies. It belongs to the exciting category of AI business automation and launchpad tools, providing the intelligent scaffolding to go from concept to reality faster than ever before. Users often explore alternatives to find a solution that perfectly matches their specific needs. This could be due to budget considerations, a desire for different feature sets like more specialized industry templates or deeper integration capabilities, or simply a preference for a different user interface and workflow. The right platform for one founder's vision might not be the ideal fit for another's. When evaluating alternatives, focus on the core value: accelerating your path to a live company. Look for platforms that offer robust AI assistance, streamline critical early-stage processes, and provide clarity without unnecessary complexity. The goal is to find a tool that feels like a co-founder, removing friction so you can focus on growth and execution.
